Apr 29, 2026
9 min read
Cloud Architect
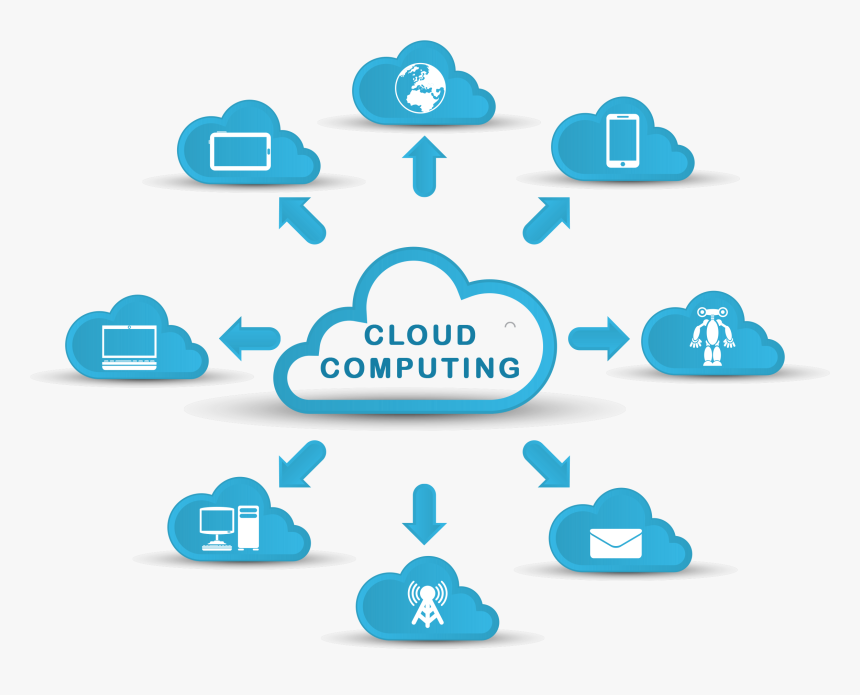
What is cloud architecture?Cloud architecture defines the fundamental components of a cloud computing environment—the front end, the back end, the networking and the delivery model—and describes how those components are combined to run a specific application or applications.Based on business needs, a cloud architecture serves as a design strategy for connecting the cloud-based infrastructure for running and deploying applications. Cloud architecture considers an organization’s workload requirements and operational costs to deliver the flexibility, scalability and cost-savings of cloud computing.Cloud architecture componentsCloud computing architecture integrates four essential components to create an IT environment that abstracts, pools and shares scalable resources across one or more cloud environments.A front-endA back-endA networkA cloud-based delivery platformCloud architectures vary based on an organization’s unique business drivers and technology requirements. Still, they all share the same goal of creating a roadmap that considers application workloads, cloud deployment models, service management and design needs.1. The front-endFront-end cloud architecture refers to the user- or client-side of the cloud computing system. It consists of graphic user interfaces (GUIs), dashboards and navigation tools that provide on-demand access to cloud services and resources. Key components include software apps and programs installed on devices (such as., mobile phone, laptop or desktop) to access the cloud platform or service. Accessing a web-based video communications application (for example, Zoom, Webex) via a laptop computer or ordering food through a mobile delivery platform (Uber Eats, DoorDash) are both examples of front-end cloud architecture capabilities.2. The back-endWhile the front-end includes all elements related to the client (for example, a visitor to an e-commerce site), the back-end (or ‘server-side’) refers to the structuring of the site and the programming of its main functionalities. It provides all of the behind-the-scenes technology (cloud servers, cloud databases, application programming interfaces (APIs) to access files) used by the CSP to support the front-end, including all the code that helps a database or web server communicate with a web browser or a mobile operating system.Back-end cloud architecture components include the following:Applications: Back-end apps are the software or platforms that deliver the client service requests on the front-end.Cloud computing service: The back-end service provides utility in cloud architecture and manages the accessibility of cloud-based resources (such as, cloud-based storage services, application development services, web services, security services, and more).Cloud runtime: Runtime provides the environment (operating system, hardware, memory) for executing or running services. Virtualization plays a crucial role in enabling multiple runtimes on the same server. (Read more about virtualization below.)Cloud storage: Cloud storage in the back-end refers to the flexible and scalable storage service and management of data stored to carry out applications.Infrastructure: Infrastructure consists of all the back-end resources or hardware (such as, servers, databases, CPU (central processing unit), network devices like routers and switches, graphics processing unit (GPU), and so on.) and all the software used to run and manage cloud-based services. In cloud-computing speak, the term infrastructure is sometimes confused with cloud architecture, but there’s a distinct difference. Like a blueprint for constructing a building, cloud architecture serves as the design plan for building cloud infrastructure.Management software: Middleware coordinates communication between the front-end and back-end in a cloud computing system. This component allows for the delivery of services in real-time to ensure smooth front-end user experiences.Security tools: Security tools provide the back-end security (also referred to as service-side security) for potential cyberattacks or system failures. Virtual firewalls protect web applications, prevent data loss and ensure backup and disaster recovery. Back-end components include encryption, access restriction and authentication protocols to protect data from breaches.3. A networkAn internet connection typically connects the front-end with the back-end functions. An intranet—a privately maintained computer network accessed only by authorized persons and limited to one institution—or an intercloud connection may also connect the back-end and front-end. A cloud network should provide high bandwidth and low latency, allowing users to continuously access their data and applications. The network must also provide agility so that access to resources can occur quickly and efficiently between servers and cloud-based environment.Other significant cloud architecture networking gear includes load balancers, content delivery networks (CDNs) and software-defined networking (SDN) to ensure data flows smoothly and securely between front-end users and back-end resources.4. Cloud-based delivery modelsThere are three main types of cloud delivery models (also known as cloud service models): IaaS, PaaS and SaaS. These models are not mutually exclusive. Most large enterprises use all three as part of their cloud delivery stack:IaaS, or Infrastructure-as-a-Service, is the on-demand access to cloud-hosted physical and virtual servers, storage and networking—the back-end IT infrastructure for running applications and workloads in the cloud. IaaS allows organizations to scale and shrink infrastructure resources as needed. This cloud-based service helps them avoid the high costs associated with building and managing an on-premises data center, providing the capacity to accommodate highly variable or ‘spiky’ workloads.PaaS, or Platform-as-a-Service, is the on-demand access to a complete, ready-to-use cloud computing platform for developing, running and managing applications. PaaS can simplify the migration of existing applications to the cloud through re-platforming (moving an application to the cloud with modifications that take better advantage of cloud scalability, load balancing and other capabilities) or refactoring (re-architecting some or all of an application using microservices, containers and other cloud-native technologies).SaaS, or Software-as-a-Service, is the on-demand access to ready-to-use, cloud-hosted application software (such as, Salesforce, Mailchimp). SaaS offloads all software development and infrastructure management to the cloud service provider. Because the software (application) is already installed and configured, users can provision the cloud-based server instantly and have the application ready for use in hours. This capability reduces the time spent on installation and configuration and speeds up software deployment.According to a Gartner report, almost two-thirds (65.9%) of enterprise IT spending will go toward Software-as-a-Service in 2025, up from 57.7% in 2022.Other popular service platforms include the following:Serverless computing (or serverless): Serverless is a cloud application development and execution model that allows developers to build and run code without provisioning or managing servers or back-end infrastructure.Business-Process-as-a-Service (BPaaS): BPaaS is a business process outsourcing platform that combines IaaS, PaaS and SaaS services.Function-as-a-Service (FaaS): FaaS is a subset of SaaS in which application code runs only in response to specific events or requests. FaaS makes it easier for DevOps and other teams to run and manage microservices applications.Key cloud architecture technologiesThe following are a few of the most critical technologies for developing cloud architecture.VirtualizationCrucial to cloud architecture, virtualization acts as an abstraction layer that enables the hardware resources of a single computer—processors, memory, storage and more—to be divided into multiple virtual computers known as virtual machines (VMs). Virtualization connects physical servers maintained by a cloud service provider (CSP) at numerous locations, then divides and abstracts resources to make them accessible to end users wherever there is an internet connection. Besides virtualizing servers, cloud technology uses many other forms of virtualization, including network virtualization and storage virtualization.AutomationCloud automation involves implementing tools and processes that reduce or eliminate the manual work associated with provisioning, configuring and managing cloud environments. Cloud automation tools run on top of virtualized environments and play an essential role in enabling organizations to take more significant advantage of the benefits of cloud computing, like the ability to leverage cloud resources on demand and scale them up and down on an as-needed basis. Automation plays a vital role in DevOps workflows, speeding up tasks related to building, testing, deploying and monitoring applications, resulting in cost savings and faster time to market.Cloud deployment modelsThere are four main cloud delivery models, each offering unique features for running workloads and optimizing business value.Public cloudA public cloud is a computing model where a cloud service provider makes computing resources (such as, software applications, development platforms, VMs, bare metal servers, and more) available to users over the public internet. CSPs sell these resources according to subscription-based or pay-per-usage pricing models.Public cloud environments are multi-tenant, where users share a pool of virtual resources automatically provisioned for and allocated to individual tenants through a self-service interface. This feature allows providers to maximize utilization of their data center hardware and infrastructure, thus offering cloud customers services for the lowest possible costs with access from anywhere.Private cloudA private cloud is a single-tenant cloud environment where all resources are isolated and operated exclusively for one organization. Private cloud combines many benefits of cloud computing with the security and control of on-premises IT infrastructure. For instance, companies that must meet strict regulatory compliance requirements, such as healthcare or financial institutions, may choose private clouds for their sensitive data using customized security measures like firewalls, virtual private networks (VPNs), data encryption and API keys.Hybrid cloudA hybrid cloud combines public cloud, private cloud and on-premises (‘on-prem’) infrastructure to create a single IT infrastructure so companies can get the best out of all computing environments to meet their business needs. Organizations favor a hybrid cloud model for its agility in moving applications and workloads across cloud environments based on technological or business goals.For instance, an enterprise with concerns surrounding sensitive data (such as, intellectual property, personally identifiable information (PII), medical records, and more) can store them in a private cloud. For other workloads, such as web hosting or content hosting, businesses may choose a public cloud setting for its cost savings and ability to scale resources up and down based on user traffic (for example, scale up during a social media campaign promoting a new product).According to the IBM Transformation Index: State of Cloud, over 77% of business and IT professionals have adopted a hybrid cloud approach.Hybrid multicloudToday, most enterprise businesses merge a hybrid cloud with a multicloud environment. A multicloud is a cloud computing model that incorporates multiple cloud services from more than one provider within the same IT infrastructure. Together, hybrid and multicloud models create a hybrid multicloud architecture that offers businesses the flexibility to create the best of both cloud computing worlds for migrating, building and optimizing applications across multiple clouds.In addition to offering the control and flexibility to choose the most cost-effective cloud service, hybrid multicloud provides the most control over where organizations can deploy and scale workloads (for example, deploy closer to edge environments), further improving performance. Each cloud provider offers its unique services. Businesses can customize a mix of network, storage and cloud solutions from different cloud providers to find the best-in-class solutions. For instance, a company may use IBM Cloud for its advanced data and artificial intelligence (AI) capabilities, Microsoft Azure for its compliance and security features and Google Cloud for its global networking reach.