Data Sovereignty in the Cloud in 2026
What is Data Sovereignty in the Cloud in 2026?
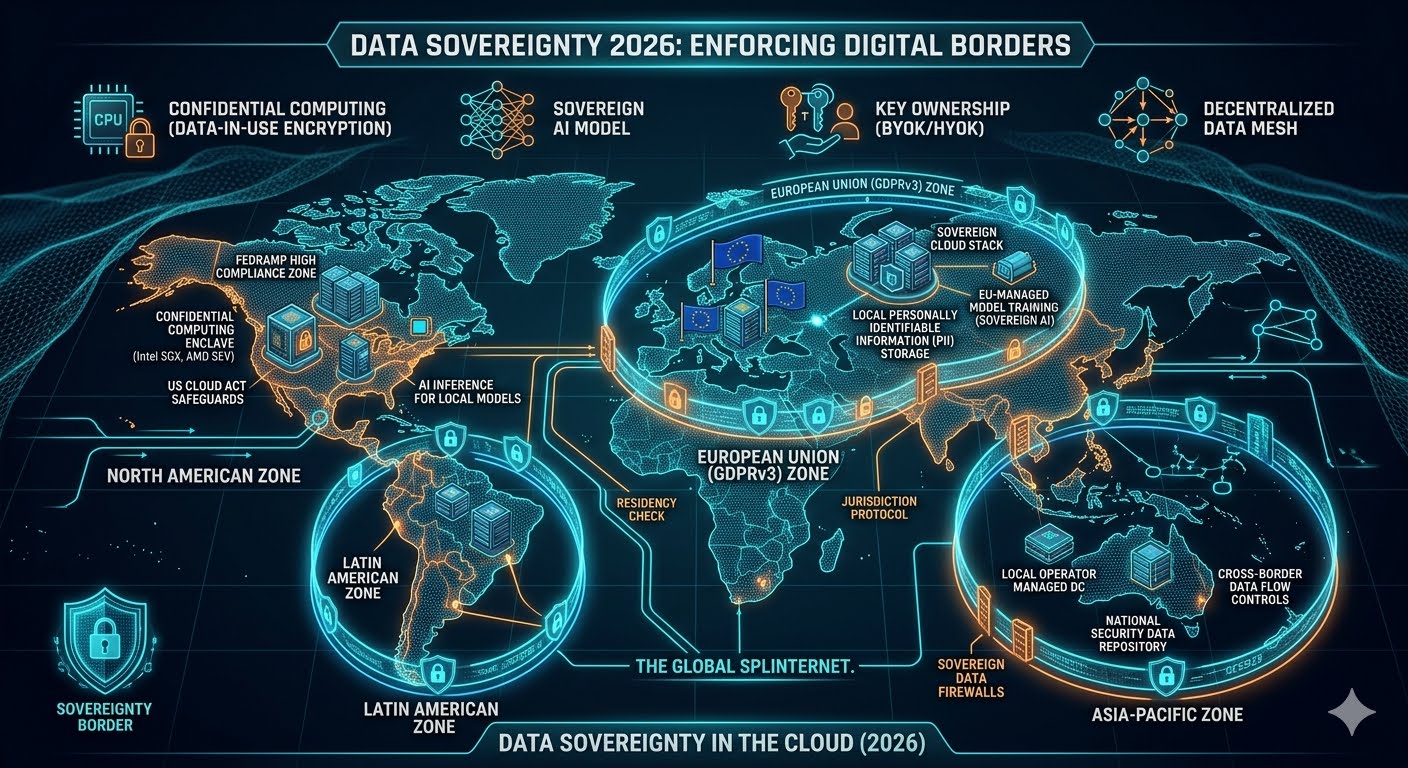
Data sovereignty in 2026 is the legal and technical enforcement of national borders on digital information, ensuring that data remains subject to the specific laws and governance of the country where it is collected or processed. As the global "Splinternet" matures, the concept has evolved from a simple legal checkbox to a fundamental pillar of cloud architecture, driven by intense geopolitical competition and the insatiable data requirements of Artificial Intelligence.
The New Reality: The Digital Border
In 2026, the idea of a borderless "global cloud" is largely a relic of the past. Nations have realized that data is the "new oil," and letting it flow unchecked across borders is a risk to both national security and economic prosperity. Data sovereignty now dictates where data is stored, who can access it, and even what hardware it is allowed to touch.
This shift has been accelerated by the "Splinternet"—a fragmentation of the internet into regional blocks (e.g., the EU, China, the US, and India) each with its own strict rules. For a DevOps or Platform Engineer in 2026, managing a global application means navigating a complex maze of contradictory regulations where a single misconfiguration can lead to massive fines or the complete shutdown of services in a region.
The Rise of the "Sovereign Cloud"
The major cloud providers—AWS, Microsoft, and Google—have responded to this demand by launching Sovereign Cloud Stacks. These are not just regional data centers; they are physically and logically isolated environments managed by local personnel and governed by local laws.
Key Characteristics of 2026 Sovereign Clouds
Feature | Traditional Cloud (Pre-2024) | Sovereign Cloud (2026) |
|---|---|---|
Data Residency | Best effort / Regional settings | Hard-enforced by local hardware |
Operational Control | Global workforce access | Local, cleared personnel only |
Encryption | Cloud-provider managed keys | User-held, local hardware security modules (HSM) |
Legal Jurisdiction | Often subject to the US CLOUD Act | Purely local jurisdiction; no cross-border warrants |
AI Processing | Global processing clusters | Localized AI inference and training |
Technological Enablers: Moving Beyond "Trust"
In 2026, organizations no longer rely on the "promises" of cloud providers. They use technical safeguards to enforce sovereignty.
1. Confidential Computing
This is the "hero" technology of 2026. Confidential Computing uses hardware-based Trusted Execution Environments (TEEs) to encrypt data while it is being processed. Even the cloud provider's administrators or the underlying operating system cannot see the data. This allows sensitive government or healthcare data to run on public cloud hardware without "leaving" the sovereign control of the owner.
2. BYOK and HYOK (Bring/Hold Your Own Key)
Standard encryption is no longer enough. Sovereignty-conscious firms now use Hold Your Own Key (HYOK), where the encryption keys never leave the company's on-premise hardware. If a foreign government subpoenas the cloud provider, the provider literally cannot hand over the data because they don't have the keys.
3. Decentralized Mesh Architectures
Modern architectures in 2026 use Data Meshes that automatically route data based on its "nationality." A user in Paris will have their data processed by a node in Frankfurt, while a user in New York will hit a node in Virginia. The application logic is global, but the data layer is strictly regionalized.
The AI Catalyst: Sovereignty in the Age of LLMs
The most significant driver of data sovereignty in 2026 is Artificial Intelligence. Nations have realized that whoever controls the data controls the AI.
"Data sovereignty in 2026 isn't just about protecting privacy; it's about protecting the intellectual property required to train the next generation of national AI models." — Industry Insight, 2026
Governments are now banning the export of certain datasets to prevent them from being used to train foreign AI models. This has led to the birth of "Sovereign AI," where countries build their own Large Language Models (LLMs) using only data that is legally and physically located within their borders. For a business, this means you might need different AI models for different regions to stay compliant.
Challenges: The Cost of Complexity
While sovereignty increases security and privacy, it comes with a "complexity tax."
Operational Overload: Managing three different "sovereign stacks" is three times as expensive as managing one global cloud.
Innovation Throttling: If data can't cross borders, it's harder for teams in different countries to collaborate on global insights.
Vendor Lock-in: Moving from one sovereign cloud to another is significantly more difficult than moving between standard public regions due to the specialized local hardware and legal wrappers involved.
The Future Outlook: A Border-Centric Digital World
As we move toward the late 2020s, the "borderless" dream of the early internet is being replaced by a more realistic, albeit more complicated, Digital Westphalianism. Organizations that succeed in 2026 will be those that don't fight this reality but instead build "Sovereignty-First" platforms from the ground up.
Platform Engineering teams are now the primary defenders of data sovereignty. By building automation that handles data residency and localized encryption by default, they allow developers to focus on features while the platform ensures the company never violates a national border.
Conclusion
Data sovereignty is the definitive challenge of the mid-2020s. It requires a total rethink of how we build, deploy, and scale software. In 2026, your data's location is just as important as its contents. By embracing confidential computing, sovereign cloud stacks, and localized AI, organizations can navigate this fragmented world without losing their ability to innovate.
Did you find this ICT insight helpful?


