Container Security in DevOps
Container Security
The shift toward cloud-native applications has made Container Security the cornerstone of modern DevOps. In a world where software is packaged into portable units like Docker or Podman, the traditional security model—protecting the physical or virtual server—is no longer sufficient. If a container is compromised, it can serve as a beachhead for an attacker to move laterally across an entire Kubernetes cluster or cloud environment.
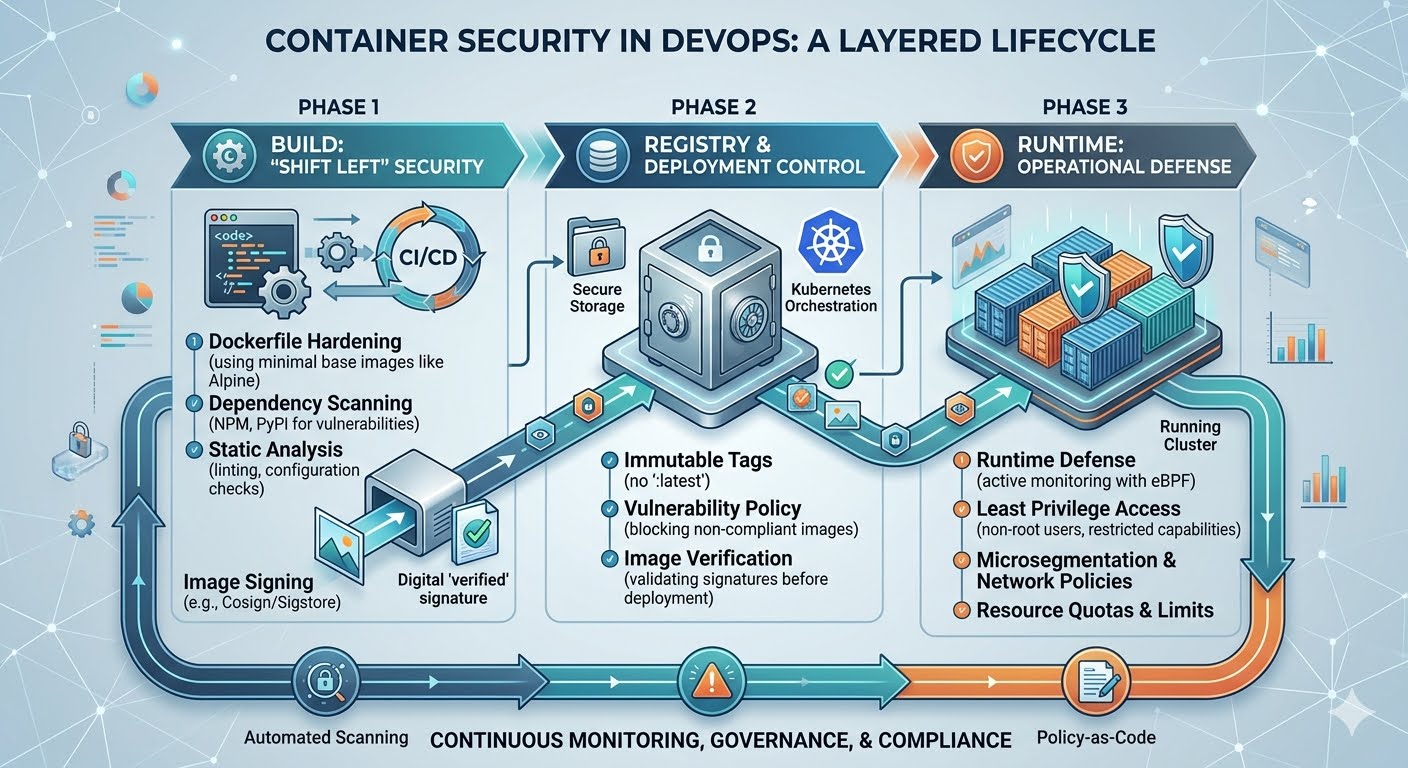
In 2026, container security is no longer a "check-the-box" activity at the end of the development cycle. It is an integrated, continuous process known as DevSecOps, where security is baked into every layer of the container lifecycle: from the moment the first line of a Dockerfile is written to the real-time monitoring of a production workload.
1. The Anatomy of Container Vulnerabilities
To secure a container, one must first understand its attack surface. A container is not a "black box"; it is a stack of dependencies, and each layer introduces potential risk.
The Base Image: Many developers pull images from public repositories like Docker Hub. If that image contains an outdated OS (like an old version of Debian) or pre-installed malicious libraries, the security of the application is compromised before a single line of custom code is even written.
Application Dependencies: Modern apps rely on hundreds of open-source packages (NPM, PyPI, Composer). These are the most common entry points for supply-chain attacks.
The Container Engine & Host: Vulnerabilities in the container runtime (like Docker or containerd) or the underlying Linux kernel can allow a "container escape," where an attacker breaks out of the container to gain control of the host machine.
Misconfigurations: Running a container as the "root" user or mounting sensitive host directories are common mistakes that turn a minor breach into a total system takeover.
2. Securing the Build Phase: "Shift Left"
The most cost-effective way to secure containers is to catch vulnerabilities during the build phase. This is the "Shift Left" philosophy in action.
Image Scanning
Every container image must be scanned for Common Vulnerabilities and Exposures (CVEs) during the CI/CD process. Tools like Trivy, Clair, or Snyk automatically analyze the layers of an image. In a mature 2026 DevOps pipeline, a "High" or "Critical" vulnerability will automatically trigger a build failure, preventing the insecure image from ever reaching a registry.
Minimalist Base Images
The "less is more" rule applies perfectly to container security. Instead of using a full-blown Ubuntu image, security-conscious teams use Distroless or Alpine Linux images. These images contain only the bare minimum files needed to run the application (no shell, no package manager, no editors), leaving an attacker with almost no tools to work with even if they manage to get inside.
3. Securing the Registry
The container registry (like Amazon ECR, GitHub Packages, or Harbor) is the "source of truth" for your infrastructure. If an attacker gains access to your registry, they can swap your legitimate images with malicious ones.
Immutable Tags: Never use the
:latesttag in production. It is ambiguous and can be overwritten. Use specific version tags or, better yet, the unique SHA-256 digest of the image.Image Signing: Using tools like Cosign (from the Sigstore project), organizations can "sign" their images. The deployment platform can then be configured to only run images that carry a valid signature from the build server, ensuring the integrity of the software.
4. Hardening the Runtime Environment
Once a container is running, the focus shifts to Runtime Defense. This is where you protect against "Zero Day" exploits that haven't been patched yet.
The Principle of Least Privilege
By default, containers should be restricted using:
Non-Root Users: Never run your application as root. If a hacker breaches a non-root container, their ability to damage the system is severely limited.
Read-Only File Systems: Configure containers so they cannot write to their own file system. This prevents attackers from downloading and executing malware within the container.
Resource Quotas: Set limits on CPU and RAM. This prevents a compromised container from being used for resource-intensive tasks like crypto-mining or launching a Denial-of-Service (DoS) attack.
Network Segmentation
In a microservices environment, containers should only be able to talk to the specific services they need. Using a Service Mesh (like Istio or Linkerd) or Kubernetes Network Policies, DevOps teams can create a "Zero Trust" network where all internal traffic is encrypted and strictly controlled.
5. Continuous Monitoring and Incident Response
Container security is not a "set it and forget it" task. Because containers are ephemeral (they might only live for minutes), traditional monitoring tools often miss them.
Modern Cloud-Native Detection and Response (CNDR) tools use eBPF (extended Berkeley Packet Filter) technology to watch what's happening inside the kernel in real-time. If a container suddenly starts making unusual network connections or attempts to modify a sensitive system file, these tools can automatically "kill" the container and alert the security team.
6. The Role of Governance and Compliance
In 2026, many industries are subject to strict regulations (like SOC2, HIPAA, or the EU's Cyber Resilience Act). Container security is no longer just a technical preference; it's a legal requirement. Policy-as-Code tools like Kyverno or Open Policy Agent (OPA) allow teams to write their security rules in code. For example: "No container may run in the 'Production' namespace unless it has been scanned in the last 24 hours." This ensures that compliance is automated and continuous, rather than a once-a-year headache.
7. Conclusion: A Layered Defense
Container security in DevOps is about Defense in Depth. No single tool or practice is a silver bullet. Instead, security is achieved through the cumulative effect of:
Scanning and signing images in the Build phase.
Securing the Registry as a trusted vault.
Applying strict Runtime policies to limit the blast radius of a breach.
As containerized environments become the standard for all enterprise software, the organizations that thrive will be those that view security not as a hurdle, but as a core feature of their delivery pipeline.
Did you find this ICT insight helpful?