The Ethics of Ransomware Payments
The Ethics of Ransomware Payments
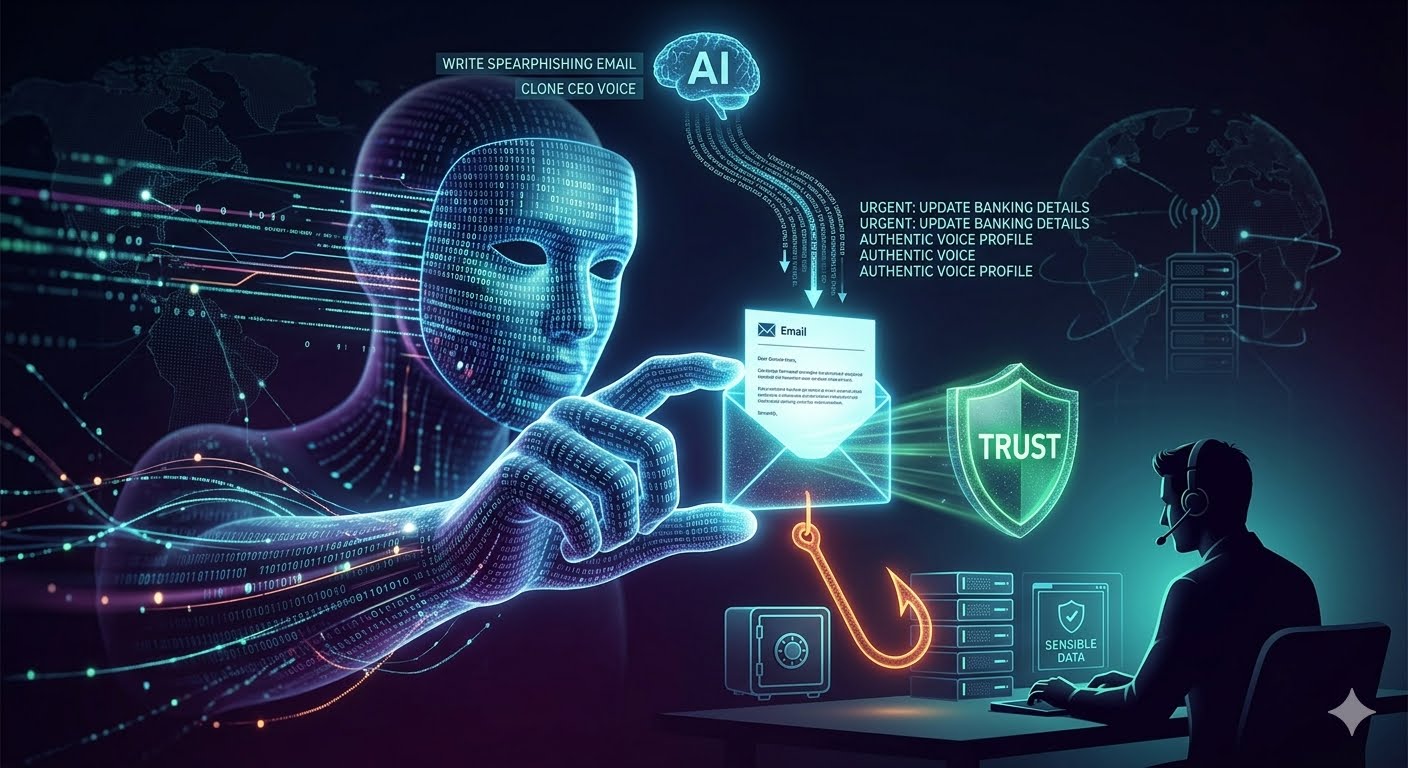
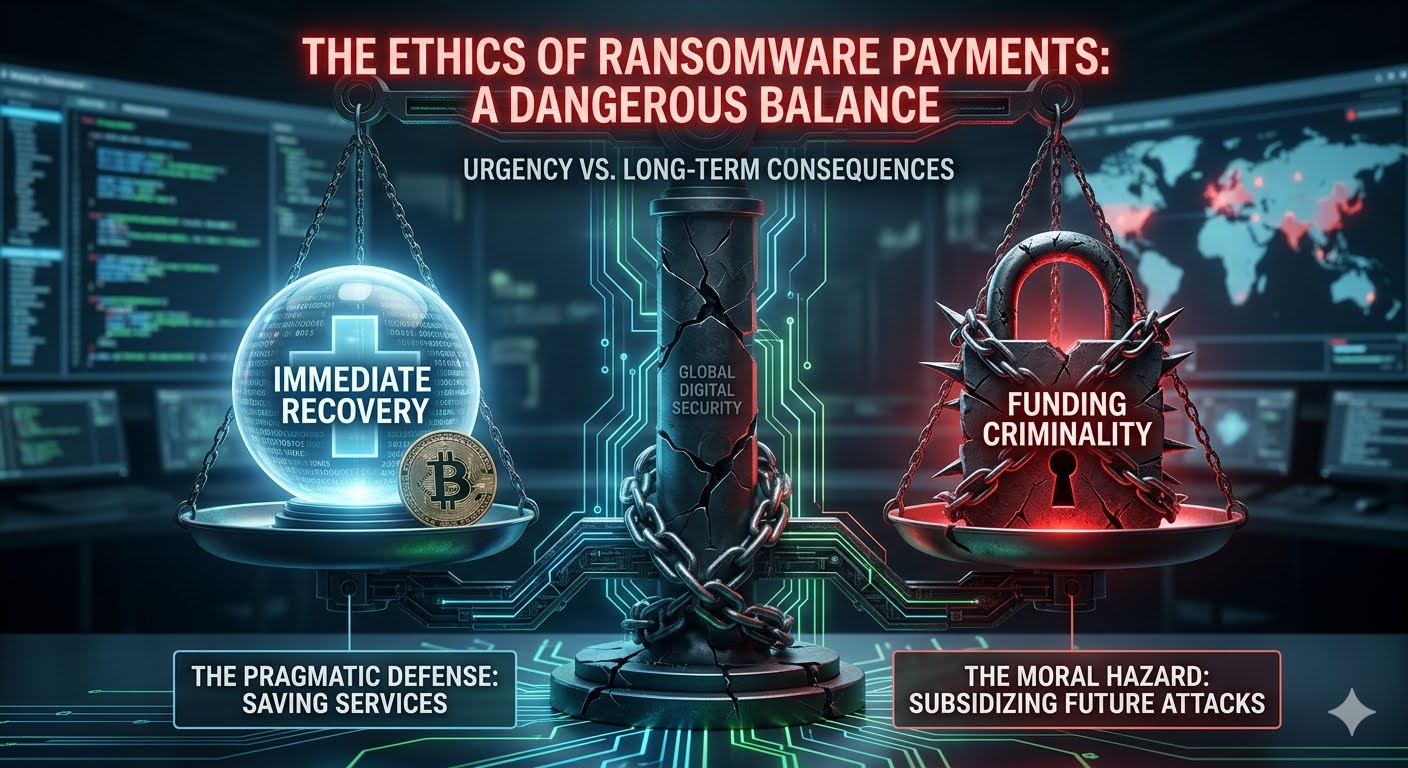
The decision to pay a ransomware demand is one of the most agonizing dilemmas in modern cybersecurity. It is no longer a purely financial calculation; it is a profound ethical crisis that pits an organization’s immediate survival against the long-term safety of the global digital ecosystem. As ransomware attacks grow in scale and severity, the debate over the morality of "buying back" data has become a central pillar of cybersecurity strategy.
The Pragmatic Defense: The Case for Paying
From a strictly utilitarian perspective, many organizations argue that paying a ransom is the "lesser of two evils." When critical infrastructure—such as a hospital, a power grid, or a municipal water system—is held hostage, the cost of inaction is measured in human lives, not just dollars.
Immediate Restoration of Services: For a hospital with encrypted patient records, every hour of downtime could mean a delayed surgery or a missed diagnosis. In such high-stakes environments, the ethical obligation to protect human life often overrides the abstract goal of de-funding cybercrime.
Fiduciary Responsibility: Corporate leaders have a legal and ethical duty to their shareholders and employees to minimize loss. If the cost of rebuilding a network from scratch is $10 million, but the ransom is $500,000, many boards see payment as the only responsible way to preserve the company’s solvency and protect thousands of jobs.
Data Sensitivity: In cases of "double extortion," where hackers threaten to leak sensitive private data (like mental health records or trade secrets), organizations may pay not just for a decryption key, but for a promise (however hollow) that the data will be deleted.
The Moral Hazard: The Case Against Paying
The counter-argument is built on the principle that "negotiating with terrorists" only fuels the fire. Law enforcement agencies, including the FBI and Interpol, strongly discourage payments because they create a self-sustaining cycle of victimization.
Funding Future Attacks: Ransomware is a business. Every dollar paid is reinvested by criminal syndicates into research and development. This allows them to buy more powerful "zero-day" exploits, recruit better talent, and target even more vulnerable sectors. By paying, a victim is essentially subsidizing the next victim’s downfall.
The "Marked" Status: Paying a ransom does not guarantee safety; it often guarantees a follow-up attack. Statistics show that organizations that pay are frequently targeted again, either by the same group or by others who see them as a "soft target" willing to open their wallet.
No Guarantee of Recovery: Attackers are under no obligation to provide a working decryption key. In many instances, the decryption tools provided are buggy and result in further data corruption, or the attackers simply vanish after receiving the cryptocurrency.
The Geopolitical and Legal Dimension
The ethics of ransomware payment are increasingly complicated by international law and sanctions. Many ransomware groups operate out of jurisdictions that are hostile to the West, and some are suspected of having direct ties to state intelligence agencies.
If an organization pays a ransom to a group that is on an official sanctions list (such as groups linked to the Russian or North Korean governments), they may be inadvertently funding state-sponsored espionage or warfare. In the United States, the Office of Foreign Assets Control (OFAC) has warned that companies facilitating such payments could face severe legal penalties, regardless of the "urgency" of their situation. This shifts the ethical burden from a private choice to a matter of national security.
The Rise of Mandatory Reporting and Bans
As the crisis deepens, some governments are moving toward a total ban on ransomware payments. The logic is that if the "revenue stream" is completely cut off, the business model of ransomware will collapse. However, critics argue that a ban would only lead to "under-the-table" payments and cause businesses to shut down permanently rather than report the crime.
A more moderate approach being adopted is mandatory reporting. By requiring companies to disclose attacks and payments, governments can gather the intelligence needed to dismantle the infrastructure (servers and crypto-exchanges) that these groups rely on.
A New Ethical Framework: "Defensive Resilience"
To move beyond the binary "to pay or not to pay" debate, the cybersecurity community is advocating for a framework of Defensive Resilience. The most ethical action an organization can take is to invest so heavily in backups and "offline" data storage that a ransom demand becomes irrelevant.
Ethical leadership in this space requires:
Transparency: Being honest with customers and regulators about the breach.
Collaboration: Sharing threat intelligence with competitors to prevent the spread of a specific strain of ransomware.
Proactive Investment: Prioritizing security budgets over "reactive" insurance policies.
Conclusion
The ethics of ransomware payments remain a "grey hat" area where there are rarely perfect answers. While the individual organization may save itself by paying, it does so at the expense of the collective security of the internet. The only true solution to this ethical impasse is to remove the leverage that attackers hold. Until organizations can recover from an attack without the need for a criminal's key, the dilemma will continue to haunt boardrooms across the globe.
Did you find this ICT insight helpful?