The Zero Trust Architecture (ZTA)
What is Zero Trust Architecture?
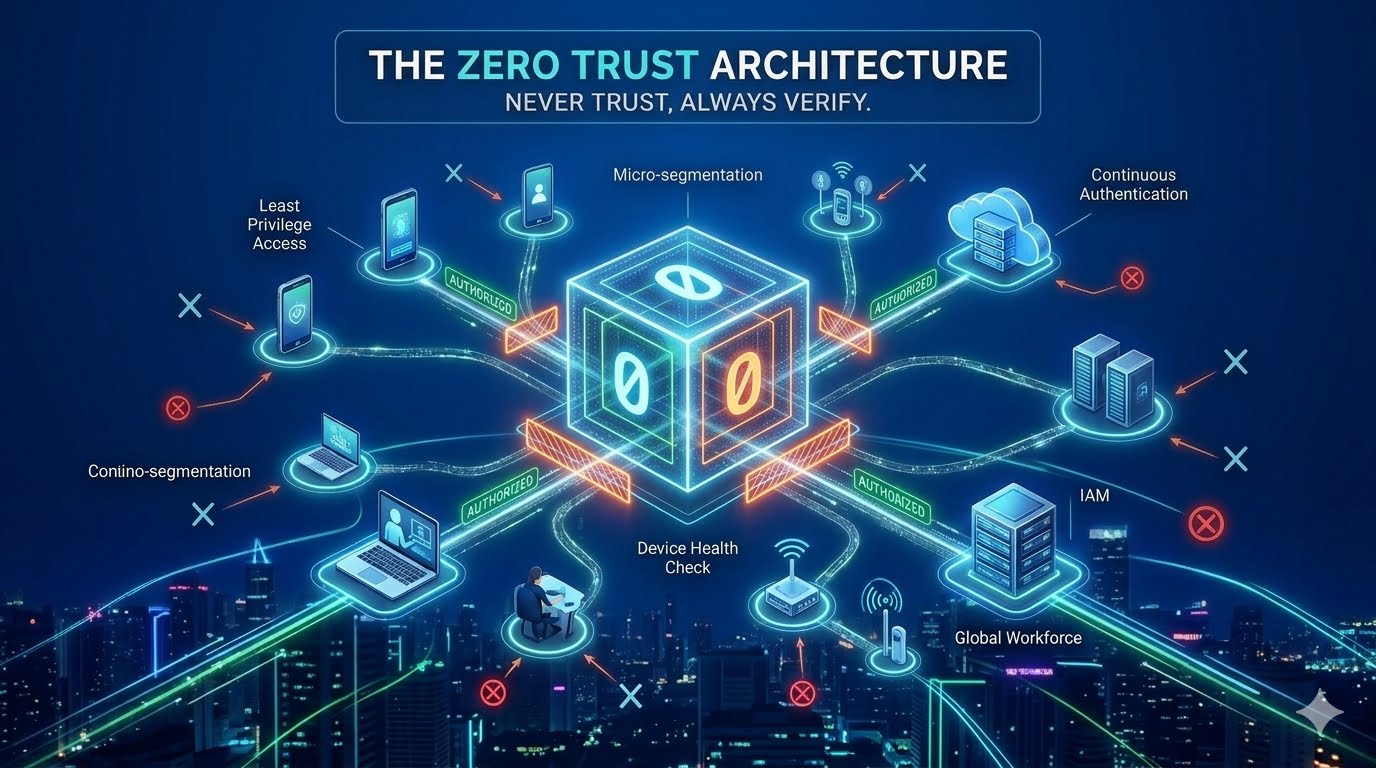
The Zero Trust Architecture (ZTA) is no longer just a buzzword in cybersecurity circles; it is the fundamental framework required to secure the modern, decentralized digital landscape. As organizations move away from traditional office-based environments toward cloud-integrated, remote-first structures, the old "castle-and-moat" security model has become obsolete. Zero Trust represents a paradigm shift from "trust but verify" to "never trust, always verify."
The Death of the Perimeter
For decades, cybersecurity was built on the concept of a hardened perimeter. If a user was inside the network (the castle), they were trusted. If they were outside, they were untrusted. This worked when all data lived in on-premise servers and all employees sat at desks in a single building.
However, the rise of Cloud Computing, Software-as-a-Service (SaaS), and Bring Your Own Device (BYOD) policies shattered this perimeter. Today, an employee might access sensitive financial data from a coffee shop using a personal tablet. In this environment, the "internal" network is no longer a safe zone. If an attacker breaches the perimeter—through a stolen password or a phishing link—they gain "lateral movement" capabilities, allowing them to roam freely through the network. Zero Trust was designed to solve this exact vulnerability.
The Core Principles of Zero Trust
Zero Trust is not a single software or product; it is a strategic framework based on three unwavering pillars:
Assume Breach: Operates under the constant assumption that the network has already been compromised. This mindset forces security teams to design defenses that limit the "blast radius" of an attack.
Verify Explicitly: Every request for access—whether from a CEO inside the office or an automated bot—must be authenticated and authorized based on multiple data points. This includes user identity, location, device health, service or workload, and data classification.
Least Privilege Access: Users are granted only the minimum level of access required to perform their specific task, and only for the duration needed. This prevents a compromised account from accessing the entire database.
How Zero Trust Works: The Components
To implement Zero Trust, organizations rely on several key technological components working in harmony:
Identity and Access Management (IAM)
Identity is the new perimeter. Strong IAM involves Multi-Factor Authentication (MFA), which goes beyond simple passwords to include biometrics or hardware tokens. In a Zero Trust environment, identity is continuously re-validated throughout a session, not just at login.
Micro-segmentation
Traditional networks are "flat," meaning once you’re in, you can see everything. Micro-segmentation breaks the network into small, isolated zones. A person in the Marketing department has no technical path to reach the Accounting servers. If a Marketing laptop is infected with ransomware, the walls of the micro-segment stay up, preventing the virus from spreading to the rest of the company.
Device Health Verification
Before granting access, the system checks the "health" of the device. Does it have the latest security patches? Is the antivirus running? Is it a recognized corporate device? If a device is deemed "unhealthy," access is denied regardless of how valid the user's password is.
Zero Trust Network Access (ZTNA)
ZTNA replaces the traditional VPN. While a VPN gives a user a "tunnel" into the whole network, ZTNA creates a 1-to-1 connection between the user and a specific application. The rest of the network remains invisible to the user.
The Benefits of a Zero Trust Approach
The primary advantage of ZTNA is a massive reduction in risk. By eliminating implicit trust, companies can stop data breaches that rely on stolen credentials or lateral movement.
Furthermore, it provides unprecedented visibility. Because every request is verified, security teams have a detailed log of who is doing what, when, and from where. This data is invaluable for compliance (like GDPR or HIPAA) and for spotting "Shadow IT"—unauthorized apps being used by employees.
Finally, it supports workforce agility. Zero Trust allows employees to work securely from anywhere in the world without the performance bottlenecks often caused by traditional VPNs.
Challenges in Implementation
Transitioning to Zero Trust is a marathon, not a sprint. The biggest hurdle is often legacy infrastructure. Older systems may not support modern authentication protocols like SAML or OIDC, making them difficult to "wrap" in a Zero Trust layer.
There is also the risk of User Friction. If security checks are too frequent or cumbersome, employee productivity drops. Organizations must balance security with "Seamless Authentication"—using signals like location and behavior to verify identity in the background without constantly prompting the user for a code.
The Future: AI and Continuous Monitoring
As we look forward, Zero Trust will be increasingly powered by Artificial Intelligence (AI) and Machine Learning (ML). Static rules (e.g., "Allow access if the user is in London") are being replaced by dynamic, risk-based scoring.
If an AI detects that a user is logging in from London at 9:00 AM, but then attempts to download 50GB of data from a server in Tokyo at 9:05 AM, the system can instantly flag this as "impossible travel" and revoke access automatically. This level of real-time, automated response is the ultimate goal of the Zero Trust journey.
Conclusion
In a world where cyberattacks are no longer a matter of "if" but "when," Zero Trust Architecture is the only logical response. By removing the concept of "trust" from the technical infrastructure, organizations can build a resilient environment that protects data even when the perimeter is breached. It requires a fundamental change in culture and technology, but for any business operating in the 21st century, it is a non-negotiable requirement for survival.
Did you find this ICT insight helpful?